What is a Hacker?
Table of Contents: Definition – Types – Hacker versus cracker – Questions from the field – Notes
Smartpedia: When dealing with computers, programmes, networks or websites, a hacker is often a person who explores the limits and mechanisms of a technology.
Hacker – a technological crossover artist
“A hacker is someone who tries to find a way to make toast with a coffee machine.” [1] This is a well-known quote that describes one version and perspective on hackers.
Another, less positively formulated version and perspective is ‘The annual damage to the German economy as a result of cyberattacks amounts to 223 billion euros’. [2]
Viewed neutrally, a hacker is simply a person who explores the limits and mechanisms of a technology, computer, programme, network or website. [3] From a critical point of view, it is not a border crosser, but a criminal person who deliberately – often for personal and/or financial motives – causes harm to people, organisations or institutions.
Similar to a journalist, the term hacker is not protected. This leads to a list of interpretations, below are some of them:
A hacker is a person who
- enjoys exploring programmed systems, gaining knowledge and building skills.
- understands circumventing or overcoming limitations as an intellectual challenge.
- programs (well) with great enthusiasm.
- knows a specific programme inside out.
- appreciates the value of hacks.
- seeks access to knowledge, information or resources that he or she and others are denied.
The person does not have to
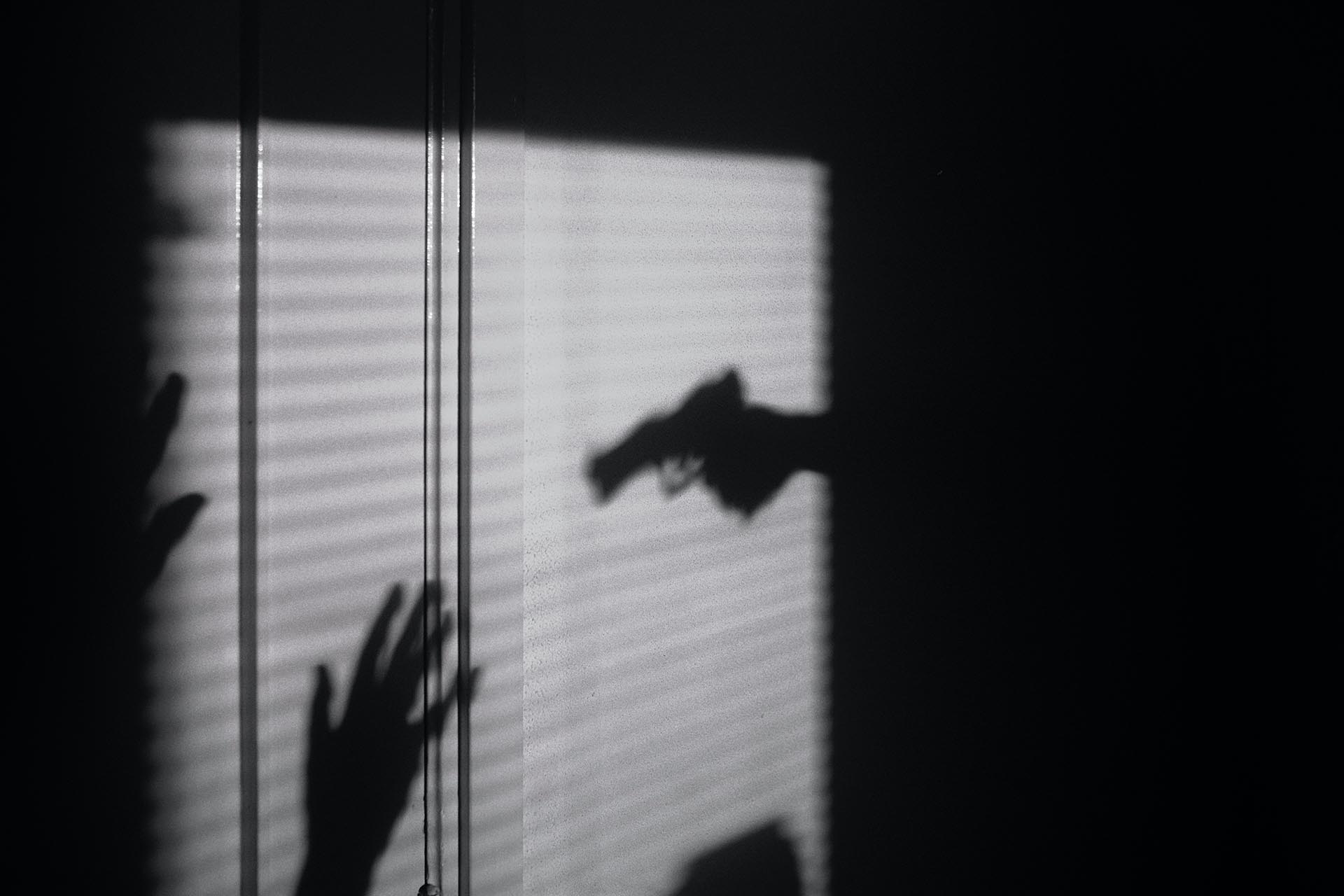
- sit in front of a computer disguised with a hoodie and/or sunglasses.
- work in a dark room lit only by the monitor light.
- be active on several computers at the same time.
- living in the single mother’s basement or garage.
In other words: there are many (pre-)judgements and clichés that are conveyed in various feature films or TV series, but must have little in common with reality. In short: there is no such thing as a typical hacker.
Types of hacker
Although there is no such thing as a typical hacker, there are usually three types:
- A black hat hacker is a person who acts with criminal intent. For example, he or she wants to steal data or install ransomware. He or she is not interested in sounding out technologies, but in maliciously crossing borders.
- A white-hat hacker is a person who penetrates a system or network but does not cause any damage. What sounds a bit strange at first glance makes sense if this person is acting on behalf of the system or network operator. Companies have a great interest in identifying and closing their own IT vulnerabilities before competitors or criminals can take advantage of them. Security authorities (usually) have an interest in protecting companies from attacks. Any sounding out of a system with its corresponding protection systems is therefore done in consultation.
(In requirements engineering, so-called misuse cases offer an approach to identify the misuse of products or functions. The aim is to derive requirements from the findings in order to make products, functions, systems, etc. more secure). - In the case of a gray hat hacker, it is not possible to directly determine the intention behind the attack on a system, network or website. In some cases, the persons involved want to publish “secret” data in order to draw public attention to grievances. In other cases, it is about blackmail, with the aim of getting organisations to take certain actions. Grey is neither white nor black, grey is grey.
The motivation is therefore decisive for the categorisation. Interestingly, this leads to a conceptual distinction that, while not universally found in common usage, is indicative of an underlying ethic:
Hacker versus cracker
In the 1980s, media became aware of hackers and focused their articles mainly on the security breaches or criminal activities committed by a few individuals. They ignored everything else that had to do with hacking. The result: the public’s perception and the self-perception of many hackers are still very different today. This misunderstanding could easily be corrected by distinguishing between hacking and cracking. A black hat hacker is a cracker, he is criminal and acts unethically. In contrast, the white-hat hacker acts like an ethical hacker [4] , for whom various principles of hacker ethics apply. These principles are named by the Chaos Computer Club [5]:
- Access to computers and everything that can show you how this world works should be unlimited and complete.
- All information must be free.
- Distrust authority – promote decentralisation.
- Judge a hacker by what he does, not by common criteria such as appearance, age, species, gender or social standing.
- You can create art and beauty with a computer.
- Computers can change your life for the better.
- Don’t trash other people’s data.
- Use public data, protect private data.
These principles of hacker ethics are intended as a guide and a basis for discussion.
Questions from the field
Here you will find some questions and answers from the field:
What is the Hacker Manifesto?
The manifesto is a short but influential text written in the form of a personal statement. It describes the thoughts and feelings of a hacker who is misunderstood by society. The text expresses the frustration of a young hacker living in a world that does not understand his curiosity and need for knowledge and instead condemns it as criminal.
Some key points of the manifesto:
- The author explains that hackers do not act out of malice or criminal intent, but out of a deep need for knowledge and understanding.
- The text highlights that society often fails to recognise the deeper motivation of hackers and is therefore quick to label them as criminals.
- The manifesto emphasises that hackers feel part of a community that looks beyond the system and tries to understand it.
- The text criticises the conventions and rules of society that restrict creativity and free thinking.
Loyd Blankenship wrote the manifesto shortly after his arrest for hacking activities. It was a reaction to the feeling of marginalisation and misunderstanding that he and many other hackers experienced. The time was characterised by increasing digitalisation and the advent of computers, which led to a new culture of hacking. At the same time, however, society was suspicious of these new ‘digital rebels’.
In the hacker scene, the manifesto has become iconic. It summarises the ethics and philosophy shared by many hackers and has inspired many young people who saw themselves in the same position as the author. It has helped to shape a positive self-image within the hacker community based on the pursuit of knowledge, freedom and innovation, rather than destruction or theft as is often assumed.
The hacker manifesto is often seen as a kind of ‘founding document’ that formulates the values of the hacker culture and defends these values against misunderstandings and prejudices. It symbolises the belief that knowledge should be free and accessible to all and that curiosity is not a crime.
Where does the term hacking come from?
The term ‘hacking’ was not originally used in connection with computers. In the 1950s, the term was used at universities such as MIT to describe creative, often unconventional solutions to technical problems. It referred to clever, original and often playful approaches to changing or improving systems, regardless of whether these systems were mechanical or electronic. Even today, hacks are often referred to.
In the early 1960s, the modern form of hacking originated at MIT, where a group of technology enthusiasts known as the Tech Model Railroad Club (TMRC) began to explore programming and early mainframe computers. These students developed a deep interest in computers and how they worked and began writing programs to explore and optimise the system. Their work consisted of testing the limits of early computer systems, finding weaknesses and finding new, more efficient ways to write programmes.
During this time, a specific ethic and culture began to emerge, which became known as the ‘hacker ethic’. This ethic emphasised the sharing of knowledge, the pursuit of efficiency and the belief that all information should be freely accessible. Hackers at MIT developed programmes and systems that often went far beyond expectations, which led to a deep rooting of the hacker mindset: to penetrate systems in order to better understand and improve them.
What is ethical hacking?
Ethical hackers go through a structured process that often includes the following steps:
- Determining the targets and gathering information about the target system.
- Using tools to scan the target system for vulnerabilities.
- Attempting to penetrate the system to test the exploitability of the identified vulnerabilities.
- Test how deeply you can penetrate the system.
- Documenting the vulnerabilities found and suggesting how to fix them.
Today, ethical hacking is a central part of cyber security. As cyber attacks become more frequent and complex, organisations and governments are increasingly reliant on regular testing of their systems to identify vulnerabilities early. Ethical hacking allows organisations to proactively improve their security measures before an actual attack takes place.
There are several prestigious certifications for ethical hackers that validate their skills and knowledge in this area, including:
- Certified Ethical Hacker (CEH): a widely used certification that certifies basic knowledge in ethical hacking.
- Offensive Security Certified Professional (OSCP): A demanding certification that confirms practical skills in penetration testing.
- GIAC Penetration Tester (GPEN): A certification that focuses on advanced skills in security testing.
You can easily find relevant training and courses by doing a little internet research.
What is a bug bounty hunter?
A bug bounty hunter is an IT security expert who specifically searches for security vulnerabilities (bugs) in software systems, applications, networks or websites and reports them to the affected companies or organisations. Bug bounty hunters receive a financial reward, known as a ‘bug bounty’, for successfully identifying and reporting security vulnerabilities.
And how do bug bounty programmes work?
Companies, especially large technology companies, set up bug bounty programmes to find security vulnerabilities in their products before they can be exploited by malicious actors. These programmes are often publicly accessible so that anyone with the appropriate skills can participate.
The size of the reward usually depends on the severity of the vulnerability discovered. Critical bugs that could cause major damage are usually rewarded more than less serious problems. Companies define the criteria for the rewards as part of their bug bounty programmes.
Each bug bounty programme has clear rules and guidelines that define what kind of tests are allowed and which systems or areas of the company are included in the tests. This prevents security tests from inadvertently causing damage or falling into legal grey areas.
Following the discovery of a security vulnerability, the bug bounty hunter creates a detailed report that describes the problem, outlines the potential risks and, ideally, makes suggestions for remediation. This report is then submitted to the organisation for review and remediation of the vulnerability.
What are well-known hacker congresses?
There are several world-renowned congresses and conventions that bring together hackers, IT security experts, activists and interested parties. These events offer lectures, workshops and competitions on various topics related to hacking, cybersecurity, data protection and technology. Here are some of the most popular:
DEF CON (Las Vegas, Nevada, USA)
DEF CON is one of the oldest and largest conferences in the world. It attracts thousands of attendees every year, including security researchers, journalists and government representatives. DEF CON offers a variety of talks, workshops, capture the flag (CTF) competitions and hacking challenges. It is known for its relaxed atmosphere and variety of topics, ranging from technical details to social and political issues.
Chaos Communication Congress (CCC) (Leipzig, Germany)
Organised by the Chaos Computer Club (CCC), the Chaos Communication Congress is one of the oldest and most important conferences in Europe. The congress takes place annually between Christmas and New Year and covers topics such as technology, society, ethics, politics and art. The CCC is known for its critical stance on surveillance and the protection of privacy.
Black Hat (USA and worldwide)
Black Hat is one of the best-known and most respected conferences in the field of information security. The event offers training and high-calibre presentations from leading experts in the industry. Black Hat is more commercially orientated than DEF CON and attracts mainly IT professionals and security companies.
ShmooCon (Washington, D.C., USA)
ShmooCon is an annual conference that takes place in Washington, D.C.. It is aimed at hackers and security enthusiasts and offers presentations on new technologies, tools and research results in the field of cyber security. The atmosphere is more informal than at the larger conferences.
HOPE (Hackers on Planet Earth) (New York City, USA)
HOPE is organised by the magazine 2600: The Hacker Quarterly and takes place every two years in New York City. The conference attracts activists, journalists and academics and covers a wide range of topics including technology, culture, politics and society.
CanSecWest (Vancouver, Canada)
CanSecWest is an annual security conference in Vancouver that focuses on advanced topics in computer security. A highlight of the conference is the ‘Pwn2Own’ competition, where participants are challenged to find and exploit security vulnerabilities in widely used software.
BSides (worldwide)
BSides is a series of security conferences held in various cities around the world. It was founded as an alternative to the larger, commercial conferences to create space for more in-depth and innovative discussions. BSides conferences are often smaller, more community-orientated and less expensive.
Hack.lu (Luxembourg)
Hack.lu is an annual security conference in Luxembourg. It provides a platform for the exchange of knowledge and research results in the field of computer security, data protection and cryptography.
RootedCON (Madrid, Spain)
RootedCON is one of the largest conferences in Spain and covers topics related to information security, network security, hacking and cybercrime. It attracts both Spanish and international participants.
These congresses and conventions are important meeting points for the hacker community and cyber security experts worldwide to exchange knowledge, learn new techniques and find out about current developments and challenges in cyber security.
What measures do you think are useful to make employees aware of the dangers of hacking?
Notes (Partly in German):
[1] The quote comes from Herwart Holland-Mortiz, also known as Wau Holland. He was a co-founder of the Chaos Computer Club.
[2] Deutsche Welle: 220 billion euros in damage due to cyber attacks.
[3] Since hacking has become a kind of popular sport and there are, for example, growth, life or trash hacks, it could also be a person who solves problems in an unorthodox way, creates workarounds or misuses products and services.
[4] Various courses or certificates on this can easily be found on the internet.
[5] Hacker ethics is based on the book Hackers – heroes of the computer revolution by Steven Levy.
[6] Phrack Magzine: Hacker’s Manifesto
If you like the article or would like to discuss it, please feel free to share it in your network. And if you have any comments, please do not hesitate to send us a message.
And here you will find additional information from the t2informatik Blog: