What is Revision Security?
Smartpedia: Revision Security addresses on the one hand a secure, verifiable archiving of data subject to retention, and on the other hand the retracing of the history of artefacts.
Revision Security – the history of artefacts
The term Revision Security refers to the archiving of information and documents that must or should be retained. In dealing with these information and documents, revision security addresses structured processes, proper use, secure operation and proof of procedural documentation. In addition, Revision Security includes the verifiability of the procedure used for storing information and documents, including the technical aids used (the electronic archive systems).
In Germany, electronic archiving systems must meet the requirements of the German Commercial Code (§§ 239, 257 HGB), the German Tax Code (§§ 146, 147 AO), the principles of proper management and storage of books, records and documents in electronic form as well as data access (GoBD) and other tax and commercial law requirements.
Criteria for revision security
The following criteria are essential for the revision security:
- regularity
- completeness
- traceability
- auditability
- safety of the overall process
- protection against change and falsification
- protection against loss
- use only by authorised persons
- compliance with retention periods
- documentation of the procedure
Distinction to traceability and IT compliance
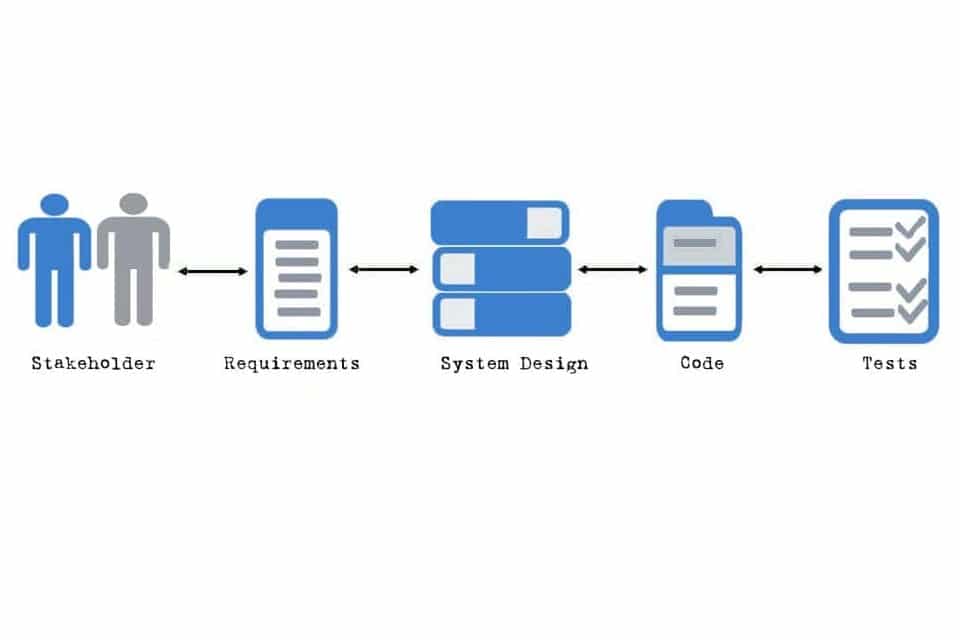
Revision Security differs from the terms Traceability and IT Compliance. In a system or software development process, Revision Security is understood as tracing back the history of artefacts, while Traceability represents the relationship between artefacts and IT compliance, i.e. compliance with processes and standards. All three terms are important, for example, in the development of security-critical software.
Notes:
If you like the article or would like to discuss it, please feel free to share it in your network. And if you have any comments, please do not hesitate to send us a message.
Here you will find additional information from our Smartpedia section: