What is a Proxy User?
Smartpedia: A proxy user in requirements engineering is a representative for users and customers who knows the wishes of customers and can empathise with them.
Proxy User – a representative for users and customers
In requirements engineering and product management, a proxy user is a representative for users and customers. He knows the wishes, expectations and goals of customers and can put himself in their shoes. This information is very important for the development of products. Of course, there are numerous possibilities to collect valid and consistent data. But stakeholder analysis, requirement workshops, field observations or interviews etc. are associated with a lot of effort and high costs. Here, a proxy user can offer support – at least to some extent.
Proxy users are persons who
- are either active users, customers, clients etc., and therefore speak for them, or
- individuals who are not active users, customers or clients, but who know them well and are close to them and their wishes up to a certain point.
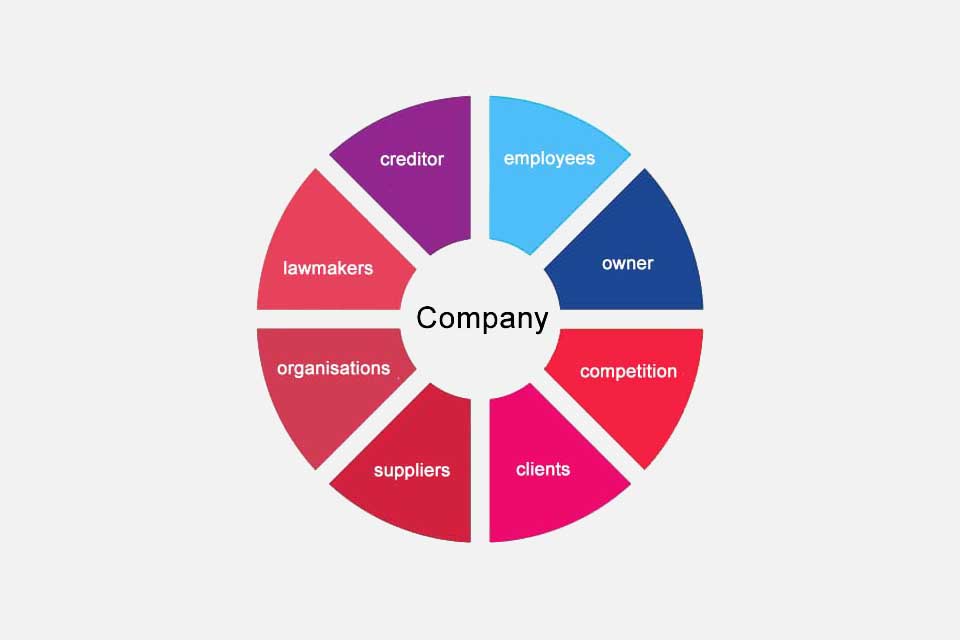
In practice, many proxy users come from the sales or support department of a company, as these areas are in regular contact with customers and users. They can therefore estimate where concrete challenges lie and what wishes are expressed. However, it is not advisable to rely only on proxy users as a source of requirements, as this way
- current problems become more important than past ones,
- only those wishes can be pursued which are known to the distribution or the support,
- and personal assessments and opinions contribute significantly to decisions.
A proxy user should therefore be regarded as a temporary addition to the requirements management process.
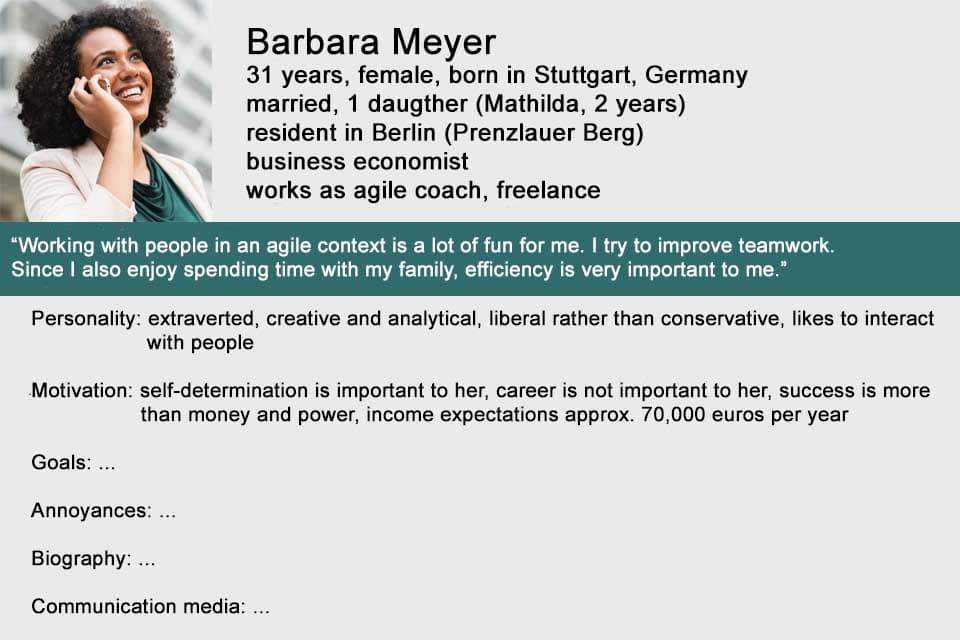
The proxy user concept should not be confused with the persona concept. Personas illustrate typical representatives of a target group. A persona has expectations, values and goals. It is the fictitious personification of a target group and helps to make assumptions about customers. A proxy user, on the other hand, is a real person who ideally knows what real existing customers need.
In the context of multi-layer software architectures, the term proxy user is also used. In most cases, users have to authenticate themselves in order to use an application or database. Since they do not want to repeat this for every application, there is the possibility to connect user accounts including their roles and rights with a proxy user, who can then access the desired information without additional authentication.
If you like the article or would like to discuss it, please feel free to share it in your network. And if you have any comments, please do not hesitate to send us a message.
Here you will find additional information from our Smartpedia section: